Cyber Security
Securing Smart Businesses with Trusted Cyber Security Services
Technology has established an arena of vast capabilities, but that does not mean everything is safe and reliable. With the proliferation of cyber threats, the need to protect the interests and assets of an organisation through the power of cyber security has become inevitable. At Webandcrafts, we help businesses with a team of cyber security experts who continuously monitor and safeguard your brand from potential threats through advanced cyber security services. We bring together a combination of in-depth business knowledge, technological excellence, and security expertise to protect, build, and nurture your organisation while ensuring a trustworthy digital world.
Cyber Security Services We Offer
We adopt a rapid and reliable approach with the best Cyber Security services for organisations to achieve their business goals. Eager to know what our expertise can contribute to your business? Here we go!
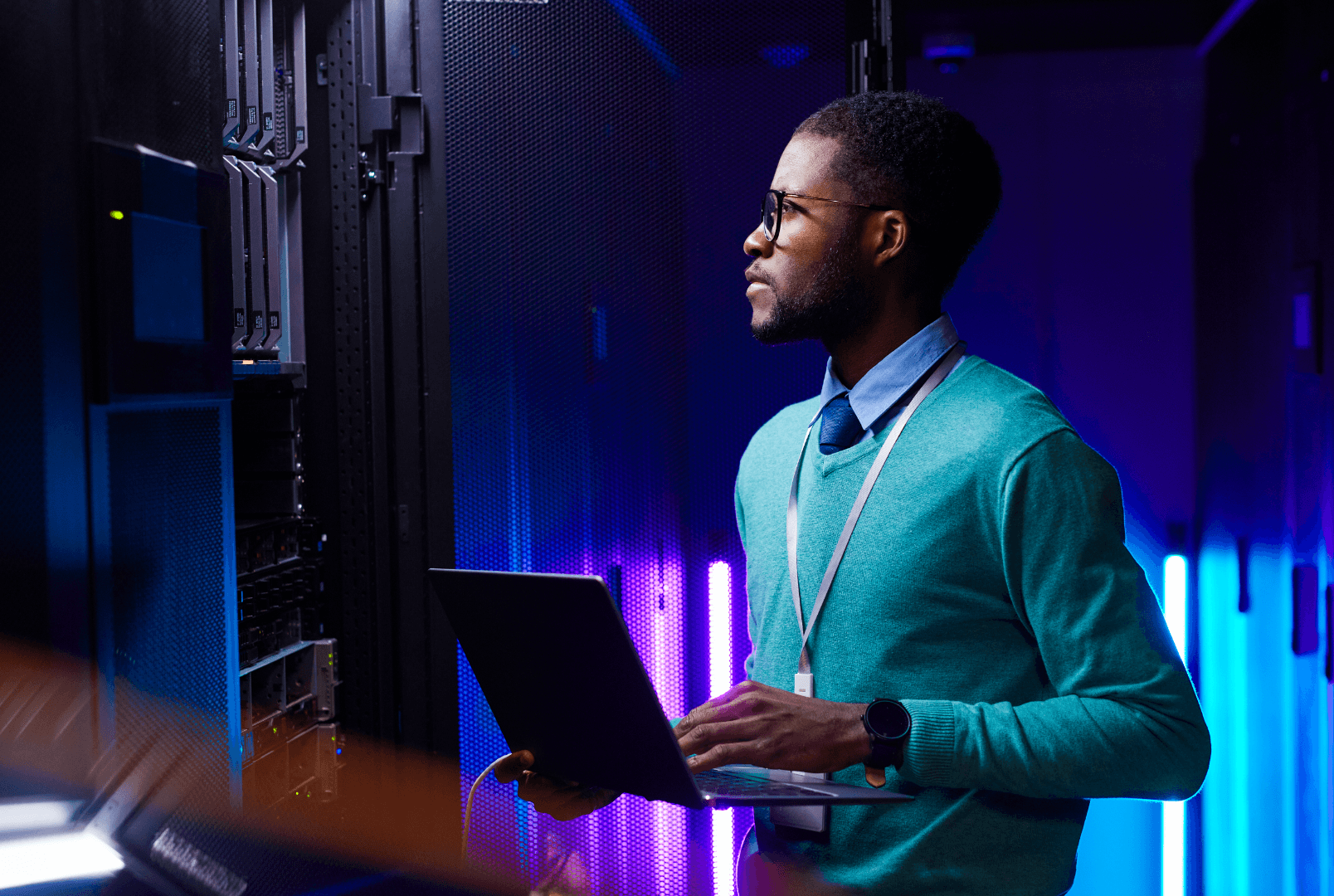
Managed Detection and Response
Monitoring and Managing Network Security
Cloud Security
Identity and Access Management
Server Security and Hardening Services
Database Hardening
Web and Mobile App Security Testing
Technical Support
Our Process
Related Industries
Our Cyber Security Case Studies
FAQ
Related Services
DevOps Consulting
Streamline software development processes and enhance the overall reliability of software delivery

Data & Analytics
Empowering businesses with data-driven insights through our comprehensive analytics services

AI & Machine Learning
Driving innovation with AI and machine learning for actionable insights and transformative outcomes

Google Cloud Platform
A suite of cloud computing services running on the same infrastructure that Google uses
Our Impact
Every innovation that happens here is out of a quest to get better at what we are already doing. We deliver ideas that make a difference, create experiences that transform lives and build ecosystems that foster progress.
Projects launched successfully across the globe
Daily customer engagement throughout our projects
Digital transformation stories that made a difference
Let’s build the future together
The future is here, and it's up to us to build it. Let's work together to create a world that is sustainable, equitable, and prosperous for all.
Insights


Blog13 mins read
Top 20 Advantages and Disadvantages of Cybersecurity

Blog5 min read
Top 10 Trending IT Jobs In India For 2026
We Are Happy to Help You
With touchpoints across numerous verticals and a passionate team at the helm, we have what it takes to give your brand the digital evolution.